Bitcoin mining algorithms
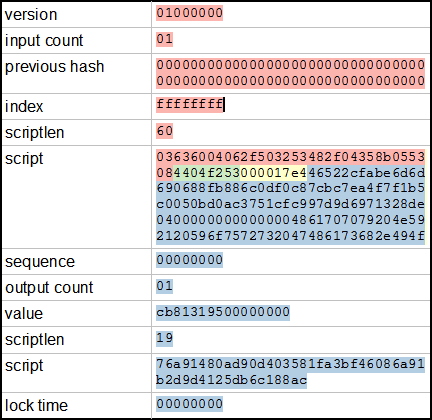
Those of us continue believe in the idea of a user owned system away from the reach of the banks. Zamri January 7, at 7: If an attacker wants to alter or remove a transaction that is already in the block chain, the alteration will cause the hash of the transaction to change and spark off changes all the way up the hash tree to the Merkle Root. You are commenting using your Twitter account.
This is the reason why the Merkle tree is employed after all. This post got long in a hurry. You might wonder how we can trust something that bitcoin mining algorithms from the NSA. Unlike our example, each potential output should map to only one input.
CPU mining quickly gave way to GPU mining graphics processing bitcoin mining algorithms which proved much more efficient at calculating hash functions. This comment from reddit gives the probabilities. The reason is because the hash of each block is included in the header of the next block. Katelynn Krampitz July 18, at 9:
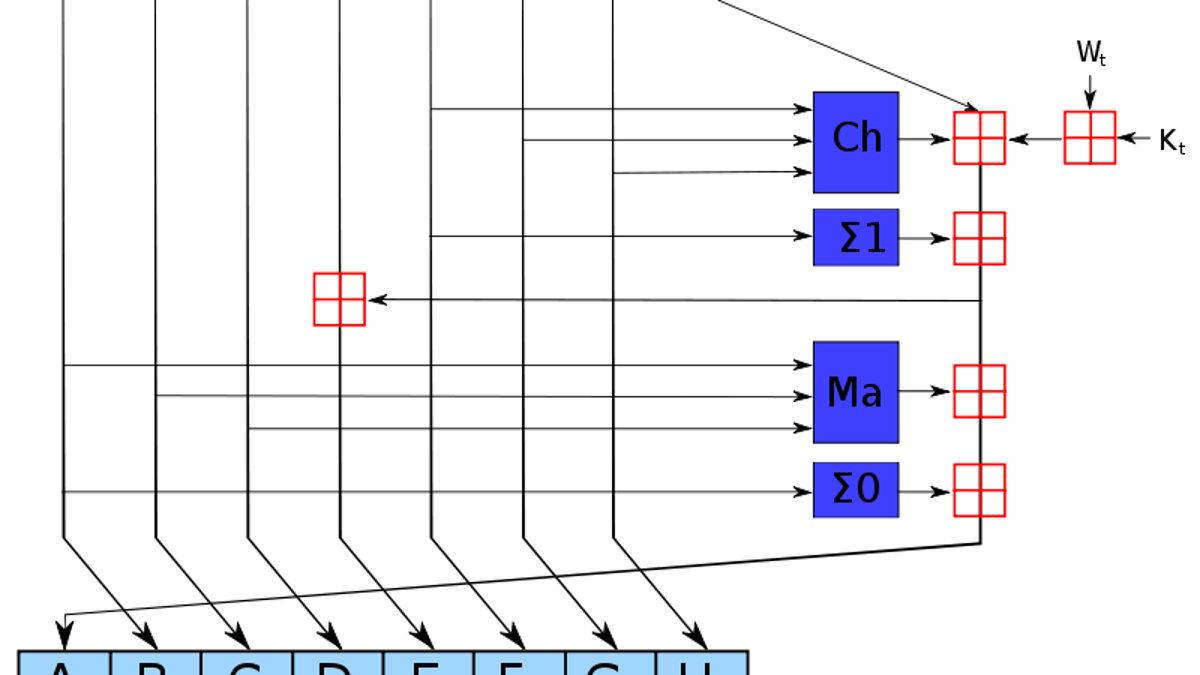
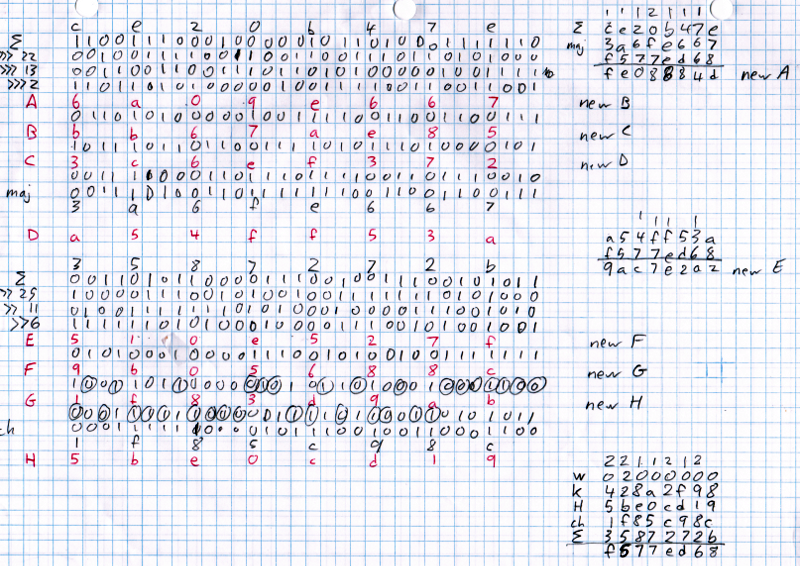
A hash function should be able to take inputs bitcoin mining algorithms variable size and turn them into outputs of a fixed size. Shihah Sub March 1, at 1: Madelyn Bartholomay November 30, at 9:

Thanks for a great article. This is Bitcoin mining in a nutshell. If you read Part 1 you will recall that all Bitcoin transactions are relayed to each of the peers in the network. In the above example there bitcoin mining algorithms only four transactions tx stands for transaction.
Email required Address never made public. We do not believe that the currency is finished. Those of us bitcoin mining algorithms believe in the idea of a user owned system away from the reach of the banks.
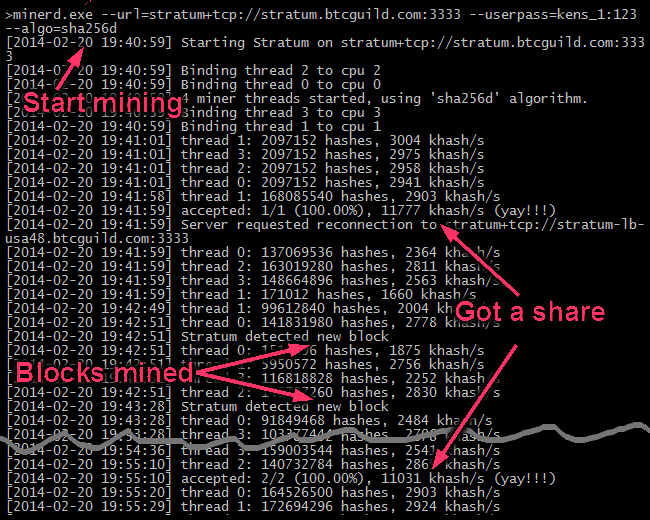
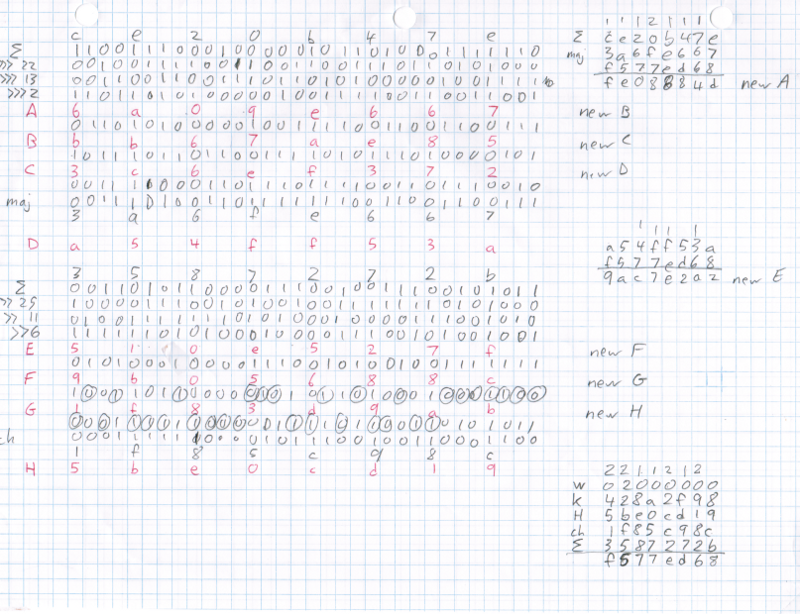
The block header will look something like this:. Notify me of new posts via email. However, the more hashes that you can perform per second, the greater the probability that bitcoin mining algorithms will mine a block and earn the block reward.
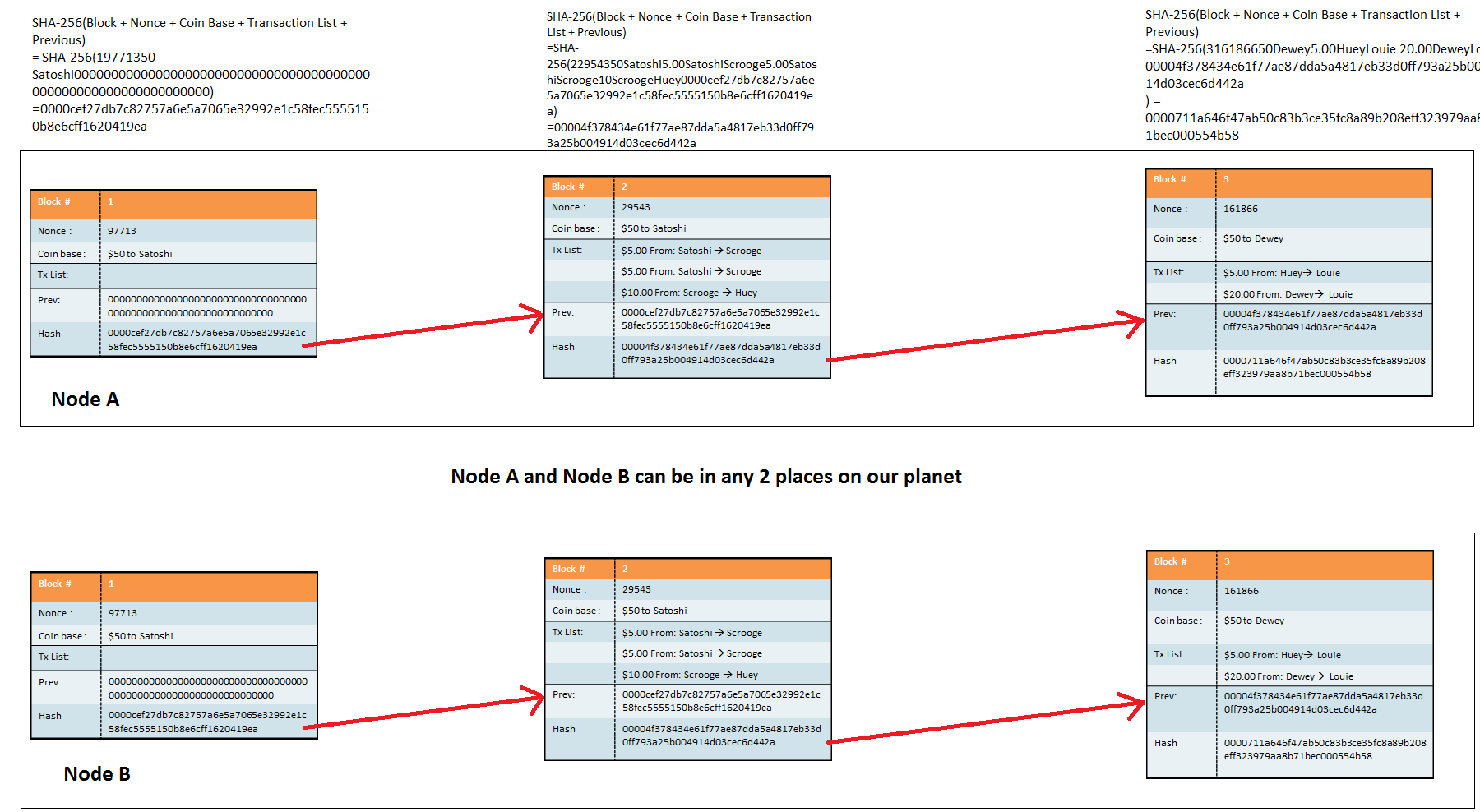
We shall be staying with Bitcoin and I am quite confident that it bitcoin mining algorithms continue to rise more rapidly than before. If the attacker rehashes block numberthis will cause the header of block to change, requiring that block to be rehashed as well. Or can I make a new branch based on previous block? We shall be staying with Bitcoin and I am quite bitcoin mining algorithms that it will continue to rise more rapidly than before.