Como ganhei r$ 712021 em 1 dia com bitcoin trade de criptomoedas
27 comments
Webbot clif hightime to buy litecoincharlie lee
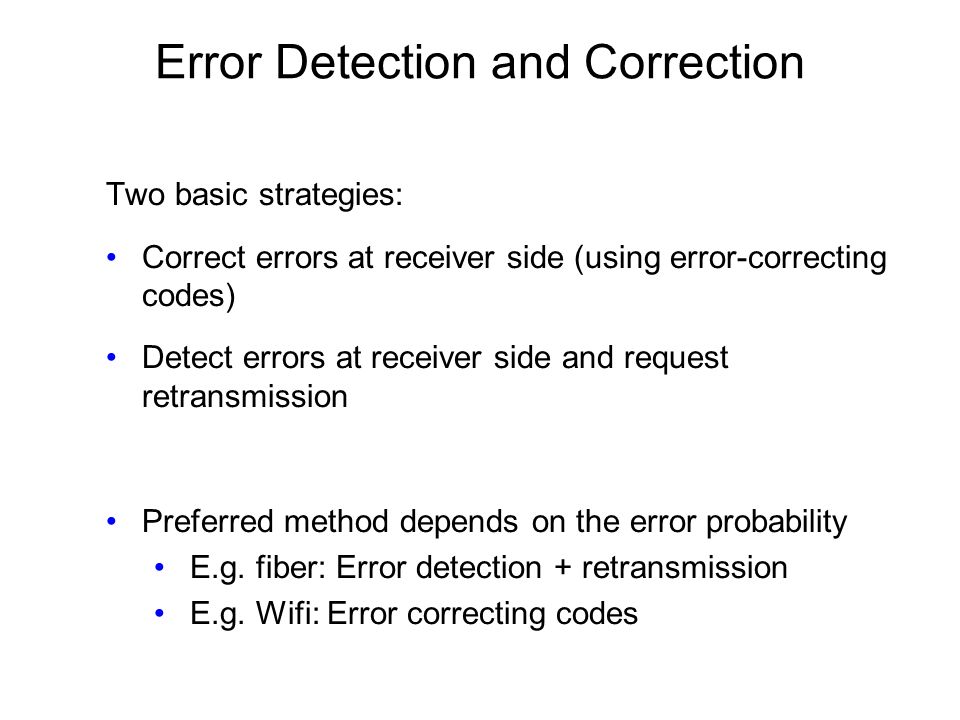
In information theory and coding theory with applications in computer science and telecommunication , error detection and correction or error control are techniques that enable reliable delivery of digital data over unreliable communication channels. Many communication channels are subject to channel noise , and thus errors may be introduced during transmission from the source to a receiver.
Error detection techniques allow detecting such errors, while error correction enables reconstruction of the original data in many cases. Error detection is the detection of errors caused by noise or other impairments during transmission from the transmitter to the receiver. Error correction is the detection of errors and reconstruction of the original, error-free data. The modern development of error-correcting codes in is due to Richard W.
The general idea for achieving error detection and correction is to add some redundancy i. Error-detection and correction schemes can be either systematic or non-systematic: In a systematic scheme, the transmitter sends the original data, and attaches a fixed number of check bits or parity data , which are derived from the data bits by some deterministic algorithm.
If only error detection is required, a receiver can simply apply the same algorithm to the received data bits and compare its output with the received check bits; if the values do not match, an error has occurred at some point during the transmission. In a system that uses a non-systematic code, the original message is transformed into an encoded message that has at least as many bits as the original message.
Good error control performance requires the scheme to be selected based on the characteristics of the communication channel. Common channel models include memory-less models where errors occur randomly and with a certain probability, and dynamic models where errors occur primarily in bursts.
Some codes can also be suitable for a mixture of random errors and burst errors. If the channel capacity cannot be determined, or is highly variable, an error-detection scheme may be combined with a system for retransmissions of erroneous data. This is known as automatic repeat request ARQ , and is most notably used in the Internet. An alternate approach for error control is hybrid automatic repeat request HARQ , which is a combination of ARQ and error-correction coding.
ARQ and FEC may be combined, such that minor errors are corrected without retransmission, and major errors are corrected via a request for retransmission: Error detection is most commonly realized using a suitable hash function or checksum algorithm.
A hash function adds a fixed-length tag to a message, which enables receivers to verify the delivered message by recomputing the tag and comparing it with the one provided.
There exists a vast variety of different hash function designs. However, some are of particularly widespread use because of either their simplicity or their suitability for detecting certain kinds of errors e. A random-error-correcting code based on minimum distance coding can provide a strict guarantee on the number of detectable errors, but it may not protect against a preimage attack.
A repetition code, described in the section below, is a special case of error-correcting code: A repetition code is a coding scheme that repeats the bits across a channel to achieve error-free communication. Given a stream of data to be transmitted, the data are divided into blocks of bits.
Each block is transmitted some predetermined number of times. For example, to send the bit pattern "", the four-bit block can be repeated three times, thus producing " ". However, if this twelve-bit pattern was received as " " — where the first block is unlike the other two — it can be determined that an error has occurred.
A repetition code is very inefficient, and can be susceptible to problems if the error occurs in exactly the same place for each group e. The advantage of repetition codes is that they are extremely simple, and are in fact used in some transmissions of numbers stations.
A parity bit is a bit that is added to a group of source bits to ensure that the number of set bits i. It is a very simple scheme that can be used to detect single or any other odd number i. An even number of flipped bits will make the parity bit appear correct even though the data is erroneous.
Extensions and variations on the parity bit mechanism are horizontal redundancy checks , vertical redundancy checks , and "double," "dual," or "diagonal" parity used in RAID-DP. A checksum of a message is a modular arithmetic sum of message code words of a fixed word length e. The sum may be negated by means of a ones'-complement operation prior to transmission to detect errors resulting in all-zero messages.
Checksum schemes include parity bits , check digits , and longitudinal redundancy checks. Some checksum schemes, such as the Damm algorithm , the Luhn algorithm , and the Verhoeff algorithm , are specifically designed to detect errors commonly introduced by humans in writing down or remembering identification numbers.
A cyclic redundancy check CRC is a non-secure hash function designed to detect accidental changes to digital data in computer networks; as a result, it is not suitable for detecting maliciously introduced errors.
It is characterized by specification of what is called a generator polynomial , which is used as the divisor in a polynomial long division over a finite field , taking the input data as the dividend , such that the remainder becomes the result.
A cyclic code has favorable properties that make it well suited for detecting burst errors. CRCs are particularly easy to implement in hardware, and are therefore commonly used in digital networks and storage devices such as hard disk drives. The output of a cryptographic hash function , also known as a message digest , can provide strong assurances about data integrity , whether changes of the data are accidental e.
Any modification to the data will likely be detected through a mismatching hash value. Furthermore, given some hash value, it is infeasible to find some input data other than the one given that will yield the same hash value. If an attacker can change not only the message but also the hash value, then a keyed hash or message authentication code MAC can be used for additional security. Without knowing the key, it is not possible for the attacker easily or conveniently calculate the correct keyed hash value for a modified message.
Any error-correcting code can be used for error detection. Using minimum-distance-based error-correcting codes for error detection can be suitable if a strict limit on the minimum number of errors to be detected is desired. The parity bit is an example of a single-error-detecting code.
An acknowledgment is a message sent by the receiver to indicate that it has correctly received a data frame.
Usually, when the transmitter does not receive the acknowledgment before the timeout occurs i. ARQ is appropriate if the communication channel has varying or unknown capacity , such as is the case on the Internet.
However, ARQ requires the availability of a back channel , results in possibly increased latency due to retransmissions, and requires the maintenance of buffers and timers for retransmissions, which in the case of network congestion can put a strain on the server and overall network capacity. An error-correcting code ECC or forward error correction FEC code is a process of adding redundant data, or parity data , to a message, such that it can be recovered by a receiver even when a number of errors up to the capability of the code being used were introduced, either during the process of transmission, or on storage.
Since the receiver does not have to ask the sender for retransmission of the data, a backchannel is not required in forward error correction, and it is therefore suitable for simplex communication such as broadcasting.
Error-correcting codes are frequently used in lower-layer communication, as well as for reliable storage in media such as CDs , DVDs , hard disks , and RAM. Error-correcting codes are usually distinguished between convolutional codes and block codes:.
Shannon's theorem is an important theorem in forward error correction, and describes the maximum information rate at which reliable communication is possible over a channel that has a certain error probability or signal-to-noise ratio SNR.
This strict upper limit is expressed in terms of the channel capacity. More specifically, the theorem says that there exist codes such that with increasing encoding length the probability of error on a discrete memoryless channel can be made arbitrarily small, provided that the code rate is smaller than the channel capacity.
The actual maximum code rate allowed depends on the error-correcting code used, and may be lower. This is because Shannon's proof was only of existential nature, and did not show how to construct codes which are both optimal and have efficient encoding and decoding algorithms.
There are two basic approaches: The latter approach is particularly attractive on an erasure channel when using a rateless erasure code. By the time an ARQ system discovers an error and re-transmits it, the re-sent data will arrive too late to be any good. Applications where the transmitter immediately forgets the information as soon as it is sent such as most television cameras cannot use ARQ ; they must use FEC because when an error occurs, the original data is no longer available.
Applications that require extremely low error rates such as digital money transfers must use ARQ. Reliability and inspection engineering also make use of the theory of error-correcting codes. Development of error-correction codes was tightly coupled with the history of deep-space missions due to the extreme dilution of signal power over interplanetary distances, and the limited power availability aboard space probes.
Whereas early missions sent their data uncoded, starting from digital error correction was implemented in the form of sub-optimally decoded convolutional codes and Reed—Muller codes.
The Voyager 1 and Voyager 2 missions, which started in , were designed to deliver color imaging amongst scientific information of Jupiter and Saturn. The Voyager 2 craft additionally supported an implementation of a Reed—Solomon code: Concatenated codes are increasingly falling out of favor with space missions, and are replaced by more powerful codes such as Turbo codes or LDPC codes.
The different kinds of deep space and orbital missions that are conducted suggest that trying to find a "one size fits all" error correction system will be an ongoing problem for some time to come. For missions close to Earth the nature of the noise in the communication channel is different from that which a spacecraft on an interplanetary mission experiences. Additionally, as a spacecraft increases its distance from Earth, the problem of correcting for noise gets larger.
The demand for satellite transponder bandwidth continues to grow, fueled by the desire to deliver television including new channels and High Definition TV and IP data.
Transponder availability and bandwidth constraints have limited this growth, because transponder capacity is determined by the selected modulation scheme and Forward error correction FEC rate. Error detection and correction codes are often used to improve the reliability of data storage media. The "Optimal Rectangular Code" used in group coded recording tapes not only detects but also corrects single-bit errors. Reed Solomon codes are used in compact discs to correct errors caused by scratches.
Modern hard drives use CRC codes to detect and Reed—Solomon codes to correct minor errors in sector reads, and to recover data from sectors that have "gone bad" and store that data in the spare sectors. Filesystems such as ZFS or Btrfs , as well as some RAID implementations, support data scrubbing and resilvering, which allows bad blocks to be detected and hopefully recovered before they are used.
The recovered data may be re-written to exactly the same physical location, to spare blocks elsewhere on the same piece of hardware, or the data may be rewritten onto replacement hardware.
DRAM memory may provide increased protection against soft errors by relying on error correcting codes. Such error-correcting memory , known as ECC or EDAC-protected memory, is particularly desirable for high fault-tolerant applications, such as servers, as well as deep-space applications due to increased radiation.
Error-correcting memory controllers traditionally use Hamming codes , although some use triple modular redundancy. Interleaving allows distributing the effect of a single cosmic ray potentially upsetting multiple physically neighboring bits across multiple words by associating neighboring bits to different words. As long as a single event upset SEU does not exceed the error threshold e. In addition to hardware providing features required for ECC memory to operate, operating systems usually contain related reporting facilities that are used to provide notifications when soft errors are transparently recovered.
An increasing rate of soft errors might indicate that a DIMM module needs replacing, and such feedback information would not be easily available without the related reporting capabilities.
One example is the Linux kernel 's EDAC subsystem previously known as bluesmoke , which collects the data from error-checking-enabled components inside a computer system; beside collecting and reporting back the events related to ECC memory, it also supports other checksumming errors, including those detected on the PCI bus.
A few systems also support memory scrubbing. From Wikipedia, the free encyclopedia. Not to be confused with error handling. This article is about computing. For knowledge, see fact checking and problem solving.